The End of Plausible Deniability
The Telephone Consumer Protection Act is not new. What is new is the carrier-level enforcement architecture, STIR/SHAKEN, which strips away the anonymity that high-volume dialers have hidden behind for years. By 2025, if your call origination isn’t properly attested, it won’t just be blocked. It will be logged, flagged, and used as evidence in enforcement actions that now carry penalties steep enough to bankrupt small operations.
This is no longer a legal problem delegated to a compliance officer. It is an engineering problem with catastrophic financial consequences.
STIR/SHAKEN: The Digital Signature on Every Call
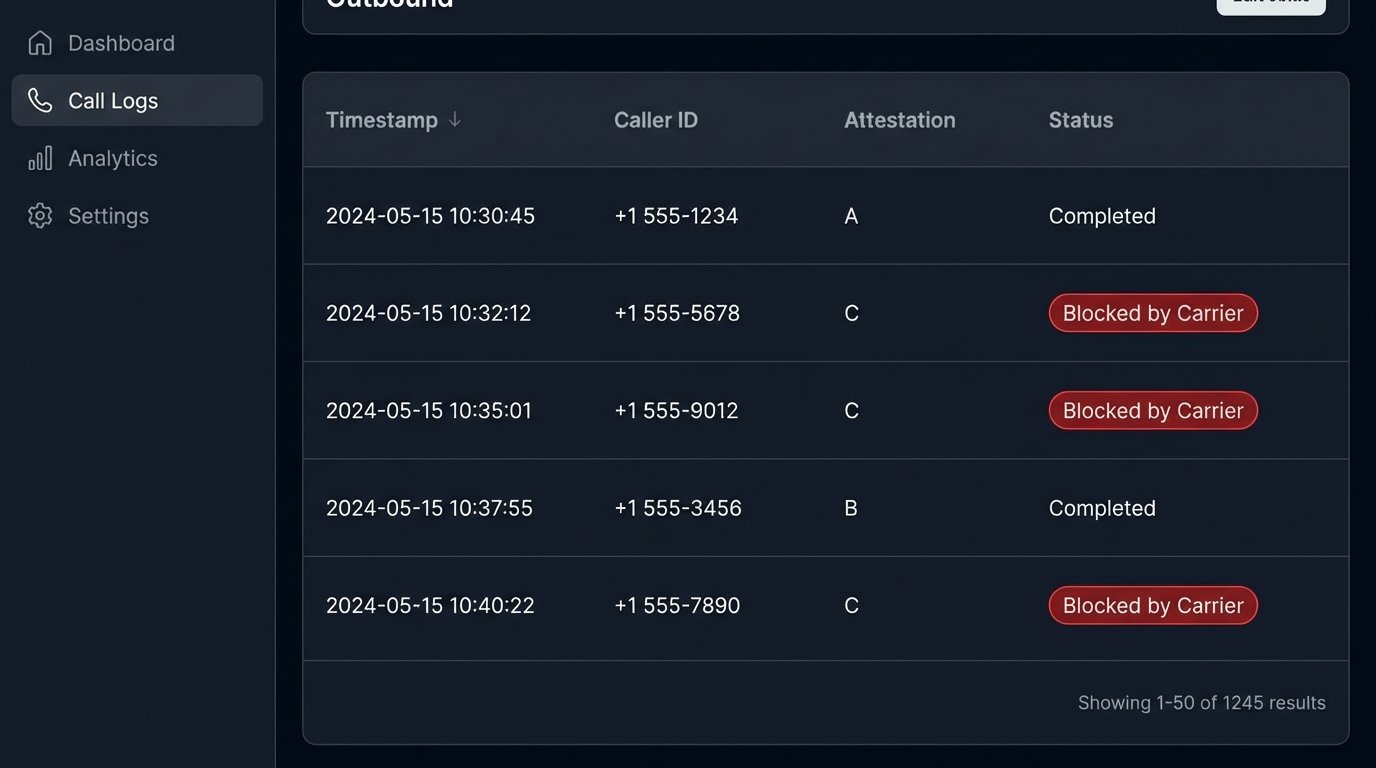
STIR/SHAKEN forces originating service providers to digitally sign every call with an attestation level. The level signals the provider’s confidence that the caller ID is not spoofed. An ‘A’ attestation means the provider knows the customer and their right to use the number. A ‘B’ means they know the customer but not their right to use the number. A ‘C’ attestation is the lowest level, meaning the provider cannot verify the call’s origin.
Terminating carriers use these attestations to decide whether to block, flag, or connect the call. A constant stream of ‘C’ level calls from your network is a massive red flag.
Your dialer’s reputation is now a quantifiable metric, and it is dropping with every unverified outbound call.
AI Dialers Under the Microscope
The term “AI Dialer” is mostly marketing fluff for predictive dialers with better algorithms. The legal definition of an automatic telephone dialing system, or ATDS, remains the core issue. The courts and the FCC fixate on whether the system has the capacity to store or produce telephone numbers using a random or sequential number generator. The ‘AI’ part doesn’t grant you a legal shield. It just makes the dialing logic more complex to defend.
Any system that dials from a list without a human agent manually initiating every single call is at risk. Arguing that your system is not an ATDS because it uses a sophisticated algorithm to predict agent availability is a fight you will likely lose.
Consent Isn’t a Checkbox, It’s a Database State
Prior express written consent is the only safe harbor for dialing mobile numbers with an ATDS. This consent must be unambiguous and specific to the type of communication. The real technical challenge is not getting the consent, but managing its lifecycle. You must be able to prove when you got it, what it covered, and most importantly, honor its revocation instantly.
A user texting “STOP” must trigger an immediate and permanent flag in your database. A verbal revocation during a call must be captured and processed by the agent into a system that prevents that number from ever entering a dialing queue again. Failure to bridge the gap between your CRM, your dialer, and your compliance database is a guaranteed violation.
This is not a task for a cron job that runs nightly. It demands real-time data synchronization.
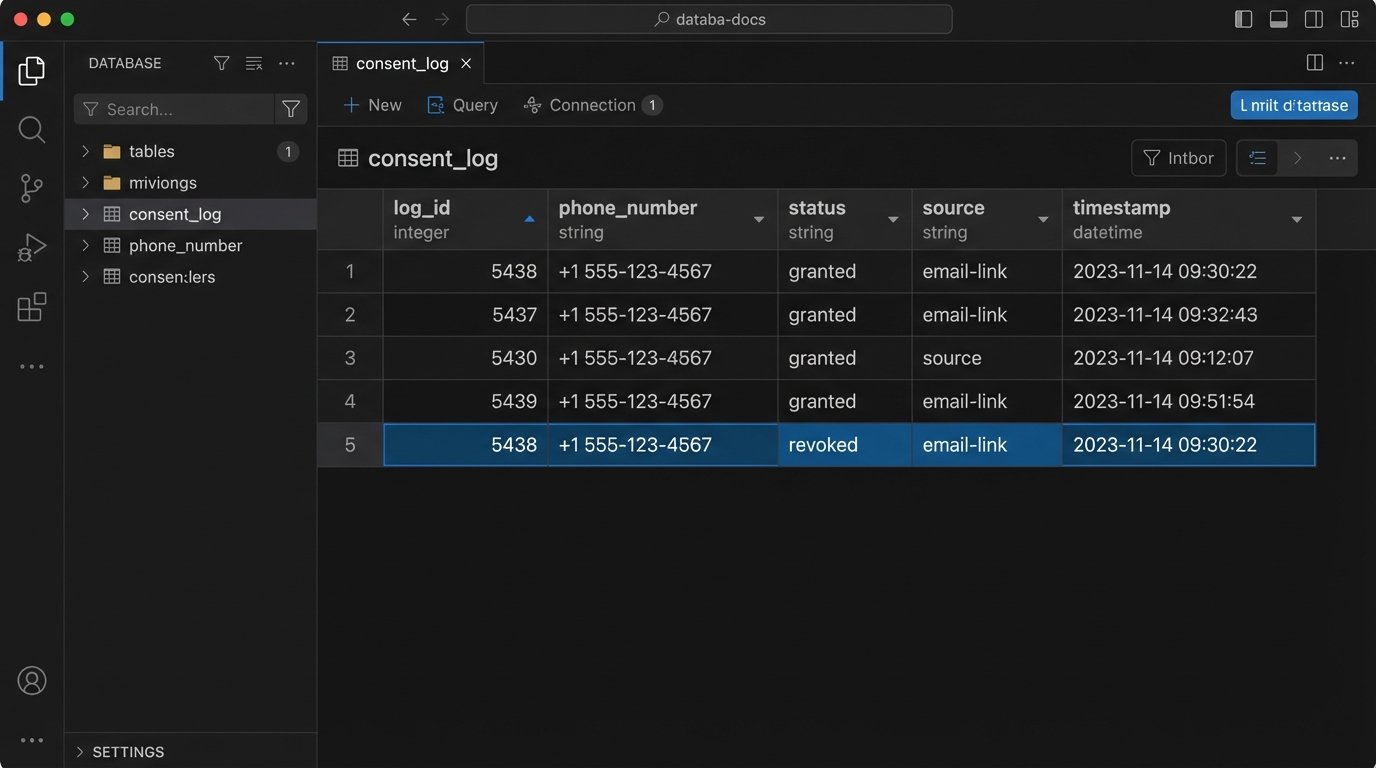
A barebones system for tracking consent requires at least a few key fields. Consider a simplified schema for a `contacts` table and a `consent_log` table. The `consent_log` tracks every change in status, creating an auditable history of permission. This is your primary evidence if a complaint is filed.
When a revocation request arrives, you don’t delete the record. You insert a new record into `consent_log` with `status = ‘revoked’`. Your dialing logic must first query this table for the most recent entry for a given phone number before ever attempting to place a call.
The logic check is simple: `SELECT status FROM consent_log WHERE phone_number = ? ORDER BY timestamp DESC LIMIT 1`. If the result is ‘revoked’, the call is killed.
Ringless Voicemail: The Failed Loophole
Ringless Voicemail (RVM) was engineered to bypass the TCPA by directly injecting a message into a carrier’s voicemail server, avoiding a “call” to the user’s handset. Proponents argued that since the phone never rings, it isn’t a call under the statute’s definition. The FCC and multiple courts have rejected this argument. They view any uninvited message delivery to a phone number as a communication subject to TCPA rules.
Relying on RVM as a compliance strategy is a massive gamble. The technology is seen as an intentional circumvention of consumer protection laws, which invites higher scrutiny and harsher penalties. The delivery mechanism is irrelevant if the recipient did not consent to the contact.
It’s an expensive way to generate complaints against your own brand.
Scrubbing Lists: A Required, Repetitive Grind
Maintaining list hygiene is a non-negotiable part of outbound operations. This involves more than just a one-time check against the National Do Not Call Registry. You must scrub lists against federal, state, and internal DNC lists before every single campaign. Numbers that were clean yesterday can be on a DNC list today. Re-using an old “cleaned” list is asking for trouble.
This process must be automated and auditable. Your system needs to log which lists were scrubbed, against which DNC databases, and when the scrub occurred. This data trail is your defense. Building a reliable data pipeline to handle this is critical. It involves fetching DNC lists, normalizing phone number formats, performing the comparison, and flagging numbers for exclusion.
Failing to update your internal DNC list in real-time is the fastest way to call someone who just asked you not to.
API-Based DNC Checks Before Dialing
For lower volume or high-value calls, a real-time API check can be a final gate before the dialer fires. This prevents calling a number that was added to a registry just hours before your campaign launch. It introduces latency and cost, but it’s cheaper than a TCPA fine.
Here is a basic Python example showing how you might structure an API call to a hypothetical DNC checking service. The key is to build your application logic to halt the call if the API returns a match or if the API call itself fails. You must default to “do not call” when verification is unavailable.
import requests
import json
# WARNING: This is a conceptual example. Do not use in production without robust error handling.
DNC_API_ENDPOINT = "https://api.dnc-service.com/v1/check"
API_KEY = "your_secret_api_key"
def is_on_dnc_list(phone_number):
"""
Checks a single phone number against a DNC API.
Returns True if on a DNC list, False otherwise.
Defaults to True in case of API failure to prevent accidental calls.
"""
headers = {
"Authorization": f"Bearer {API_KEY}",
"Content-Type": "application/json"
}
payload = {
"phoneNumber": phone_number
}
try:
response = requests.post(DNC_API_ENDPOINT, headers=headers, data=json.dumps(payload), timeout=2)
# Logic-check the response status.
if response.status_code == 200:
data = response.json()
# The API's response structure dictates this key.
return data.get("isOnDncList", True)
else:
# Any non-200 response is treated as a failure.
print(f"API Error: Status code {response.status_code}")
return True
except requests.exceptions.RequestException as e:
# Network errors, timeouts, etc.
print(f"Request failed: {e}")
return True
# --- Dialing Logic ---
lead_number = "2024561111"
# The final gate before placing the call.
if not is_on_dnc_list(lead_number):
print(f"Number {lead_number} is clean. Proceeding to dial.")
# Place dialer API call here.
else:
print(f"Number {lead_number} is on a DNC list or could not be verified. Call aborted.")
This script is a simplified model. A production system needs batch processing capabilities, sophisticated retry logic for transient network errors, and comprehensive logging for audit purposes.
The timeout parameter is not optional.
The 2025 Reality: Zero Trust for Outbound Calls
The trajectory is clear. Carriers are being forced by the FCC to become more aggressive in policing their networks. Call blocking and labeling algorithms are getting smarter. They analyze call duration, answer rates, and complaint data to build reputation scores for originating numbers. Your call deliverability is now a direct reflection of your compliance.
Operations that treat compliance as a checklist to be completed once will see their answer rates collapse. The new environment demands a “zero trust” approach. Every number on every list must be treated as hostile until it is verified, its consent status is confirmed, and the call itself is properly attested.
The days of buying a list and letting a dialer run unchecked are over.