Automating an e-signature workflow is not about connecting two APIs. It’s about building a stateful, auditable system that can withstand network failures, bad data, and bad actors. The vendor’s documentation describes a perfect world. We are paid to architect for the one that actually exists, where APIs go down and payloads are malformed.
The goal is not just to get a document signed. The goal is to create a legally defensible record of that signing event. Every line of automation code that touches this process either strengthens that record or invalidates it completely. There is no middle ground.
Isolate Your API Credentials Immediately
Leaving API keys in a config file or environment variable is amateur hour. These credentials are the keys to an engine that generates legally binding agreements. Treating them like a database password is a critical mistake. Any credential with that power requires a proper secrets management system like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault.
The system should force programmatic, short-lived access. Your application authenticates to the vault, gets a temporary token, and uses that to fetch the e-signature API key. This isolates the credential and gives you a clear audit log of every time it’s accessed. Manual key rotation becomes a relic of the past.
This isn’t about just preventing leaks. It’s about being able to prove who accessed what, and when, after a security incident has already happened.
Deconstruct and Validate Every Outbound Payload
The e-signature platform’s API is not a data validation service. It expects a clean, correct payload. Sending it garbage can result in documents going to the wrong recipients, containing incorrect data, or failing silently. The time to logic-check your data is before it ever leaves your server and becomes an API call.
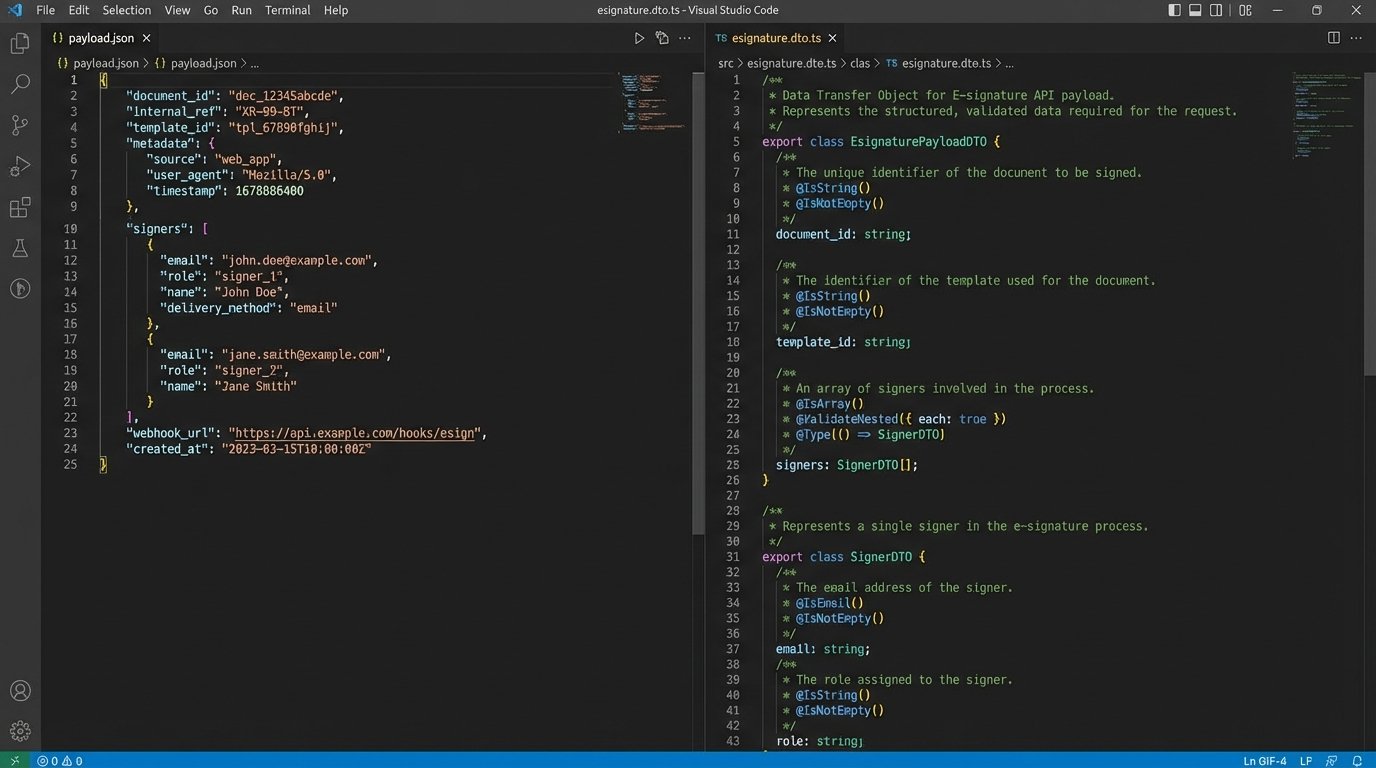
This means stripping all data down to its required primitives. Map your internal data models to a rigid DTO (Data Transfer Object) specifically for the API payload. This DTO should enforce data types, lengths, and formats. If the API expects a ISO 8601 date string, your code should reject anything else before the payload is even constructed.
Failing to do this means you’re trusting upstream data sources, which is a bet no experienced engineer should ever make.
Architect for Idempotency from Day One
Network connections fail. Servers return 503s. Your workflow will inevitably need to retry operations. If you send the same API call to create a signing request twice, you get two signing requests. This confuses users and corrupts your internal state. You solve this by using an idempotency key.
Most competent e-signature APIs support an `Idempotency-Key` header. This is a unique value, typically a UUID, that you generate and send with the request. If the API server sees the same key twice for the same operation, it doesn’t execute the operation again. It just returns the result from the first successful request.
A Minimal Request Structure
Your API client must be built to generate and track these keys. When a request is initiated, generate a UUID and store it with the status of your internal document record, marking it as `PENDING_API_CALL`. If the call fails and you retry, you re-use the exact same key. This turns a dangerous operation into a safe one.
POST /api/v1/signature_requests
Content-Type: application/json
Idempotency-Key: a3d2c8f1-b4e5-4a67-8c19-d0f9a2b7e3d0
{
"document_id": "doc_12345",
"template_id": "tpl_abcde",
"signers": [
{
"name": "Jane Doe",
"email": "jane.doe@example.com",
"role": "Primary Signer"
}
],
"metadata": {
"internal_ref_id": "txn_98765"
}
}
This isn’t a feature. It’s a mandatory architectural component for any serious transaction processing system.
Your Webhook Endpoint Is a Publicly Exposed Backdoor
Relying on webhooks for status updates is standard practice. An e-signature platform will POST to your endpoint when a document is viewed, signed, or declined. This endpoint is, by definition, open to the internet. Treating it as a trusted source of information is a catastrophic security failure. Every inbound request to this endpoint must be treated as hostile until proven otherwise.
Securing this ingress point is like trying to filter a river for a specific drop of water. You need multiple layers of verification to prevent bad data injection or malicious attacks. Simply accepting the JSON and updating your database is asking for a breach.
Signature Verification is Not Optional
Any respectable webhook provider signs their requests, usually with an HMAC signature passed in a header. You must validate this signature on every single request. The process is straightforward: concatenate parts of the request (like the timestamp and the raw body) and run it through the same hash function with your shared secret. If the signature you generate matches the one in the header, the request is authentic.
If you don’t perform this check, anyone on the internet can craft a fake POST request to your endpoint and mark a fraudulent contract as “signed” in your system.
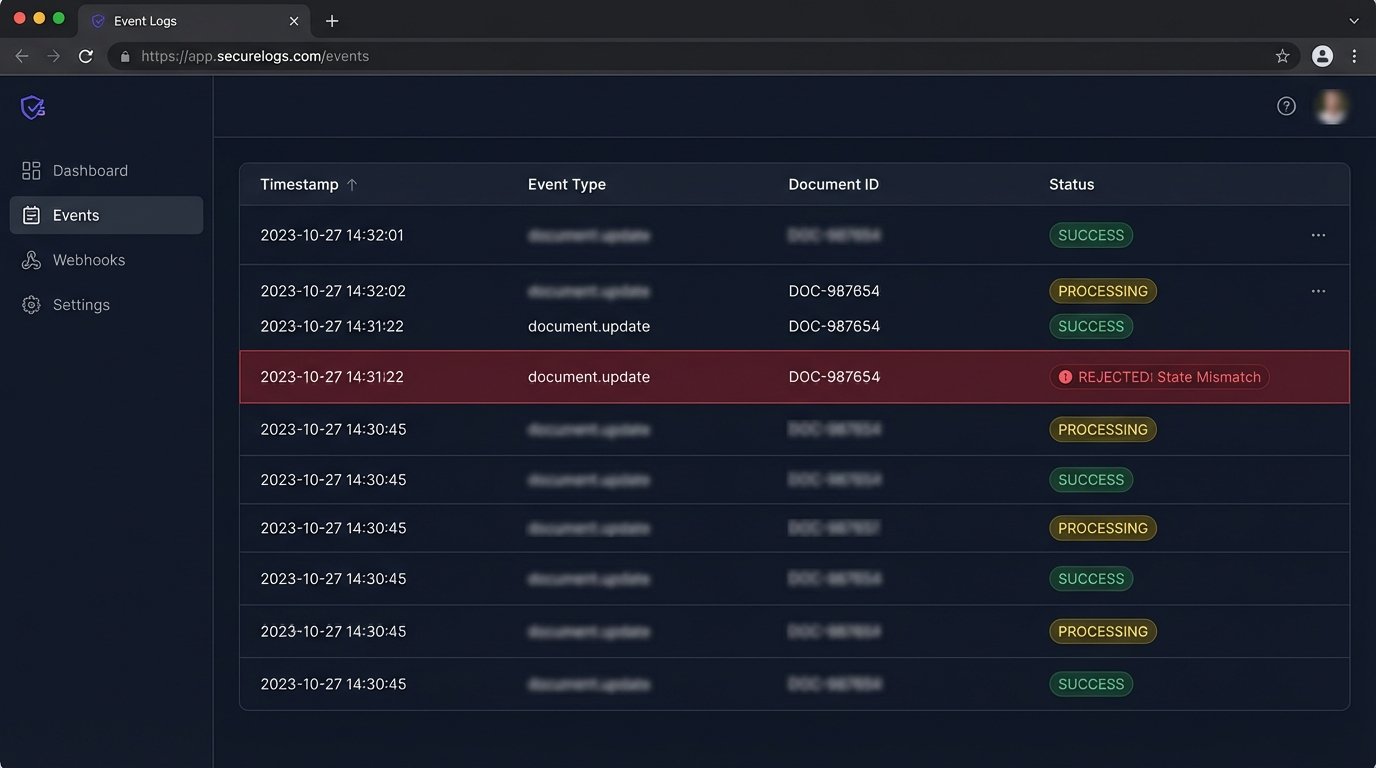
Logic-Check the Payload Against Your Internal State
Authenticity isn’t enough. The data itself must be plausible. When a webhook arrives stating `document_id: 123` was signed, your first step is to check your own database. Does a document with ID 123 exist? Is its current state `SENT_FOR_SIGNATURE`? If your system thinks that document is still in `DRAFT` status, the webhook is either out of order or fraudulent. Reject it.
Never trust the event payload to be the sole source of truth. It is merely a signal that you should check the API for an authoritative update.
The Audit Trail is the Product, Not the PDF
The signed PDF is just a user-friendly receipt. The legally binding asset is the audit trail. This trail is a meticulous log of every event in the document’s lifecycle: who it was sent to, their IP address, when they viewed it, what device they used, and the cryptographic proof of their signature. Your automation’s primary job is to securely ingest and preserve this trail.
Losing the audit trail is equivalent to losing the signed contract. Your automation must be designed to pull this data, verify its completeness, and store it in a way that guarantees its integrity over time. Storing it in a regular database table is insufficient.
This process is like assembling a complex machine in a zero-gravity environment. Each piece must be perfectly placed and locked down before moving to the next, otherwise the entire structure floats apart.
Ingest, Verify, and Store Immutably
Upon receiving the final “signed” webhook, your system should trigger a job to fetch the full audit trail from the provider’s API. Once retrieved, you must verify it. Does it contain all the expected events? Are the signer details correct? After verification, this trail should be stored in an immutable format. Think WORM (Write Once, Read Many) storage like an S3 bucket with object locking enabled.
This ensures that once the record is stored, it cannot be altered, providing a clear chain of custody required for legal proceedings.
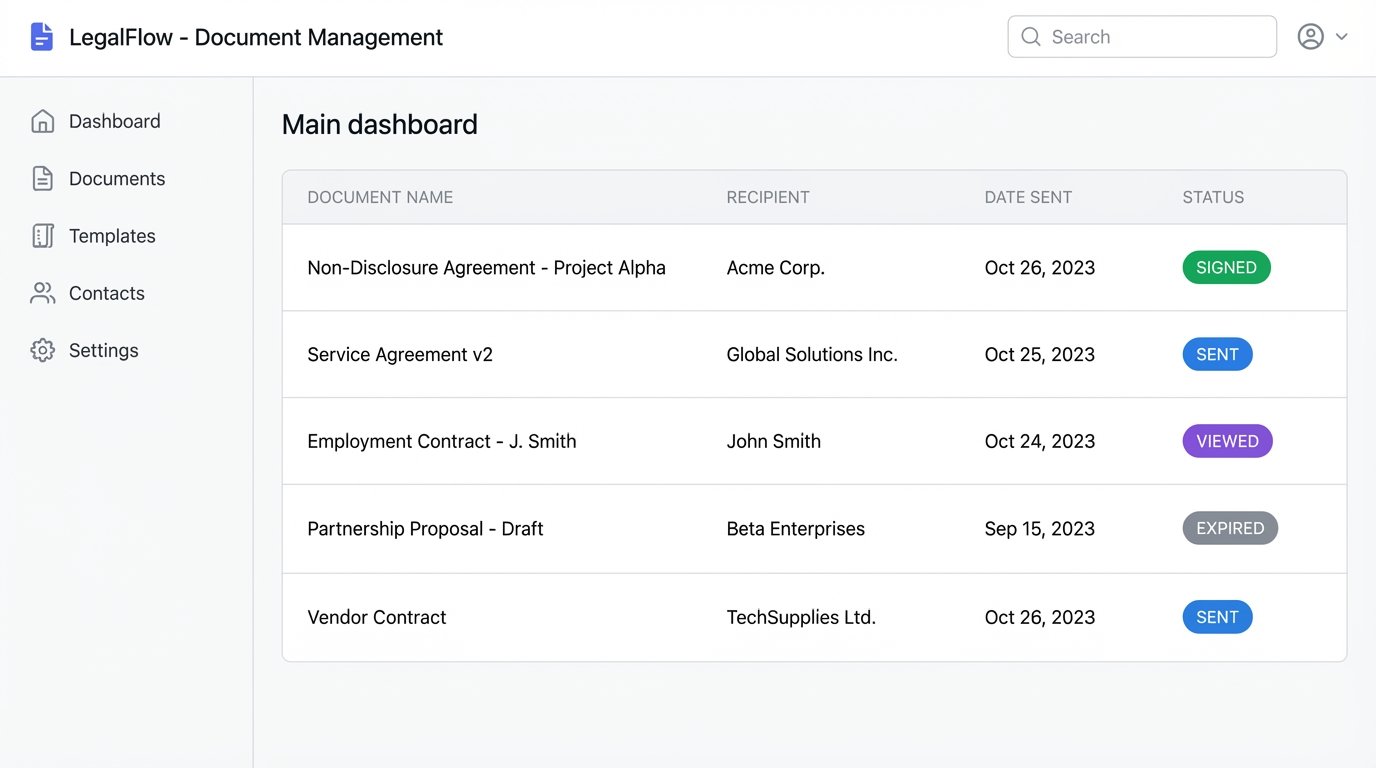
Build a Real State Machine
A boolean `is_signed` flag is not state management. A document has a complex lifecycle, and your automation must track it accurately. You need a finite state machine to model the possible states: `DRAFT`, `CREATING`, `SENT`, `VIEWED`, `SIGNED`, `DECLINED`, `EXPIRED`, `DELIVERY_FAILED`. Every API call and webhook event is a transition between these states.
This model allows you to handle edge cases correctly. What happens if a document expires? Your state machine transitions it to `EXPIRED` and can trigger a notification. What if an email to a signer hard bounces? The platform might send a `DELIVERY_FAILED` event, allowing you to flag the document for manual review.
Without a proper state machine, your system will inevitably end up with orphaned documents stuck in limbo, requiring manual database intervention to fix.
Interrogate the Vendor’s SDK
Using the official SDK for the e-signature platform is convenient. It can also be a black box that hides critical behavior. Many SDKs have built-in retry logic that is poorly documented or unconfigurable. This can lead to the exact duplicate request problem that idempotency keys are meant to solve, as the SDK might retry a request that timed out on the client side but actually succeeded on the server.
Before putting an SDK into production, you must observe its behavior. Put it in a test harness and use a tool to inspect the raw HTTP requests it generates. Watch what it does during a simulated network failure. How does it handle a 429 rate limit response? Does it back off exponentially or just hammer the API?
Trusting an SDK without this level of inspection means you are letting a third-party’s code dictate the reliability of your core business logic.
The ultimate goal is an automated system that fails predictably. When a signature workflow breaks, it should do so loudly, clearly, and in a state that can be safely resumed or remediated. Silent failures in document processing don’t just create bugs; they create legal liabilities.
